NemoClaw Tames the 320k-Star OpenClaw Beast
NVIDIA's sandboxed runtime, declarative policies, and human-in-the-loop approvals turn viral autonomous agents into something you can actually run in production.
- NemoClaw turns the viral but dangerously unrestricted OpenClaw agents into production-ready systems through a single curl-installed stack.
- Declarative YAML policies with hot-reloadable network and inference rules combined with immutable filesystem and process rules provide precise control.
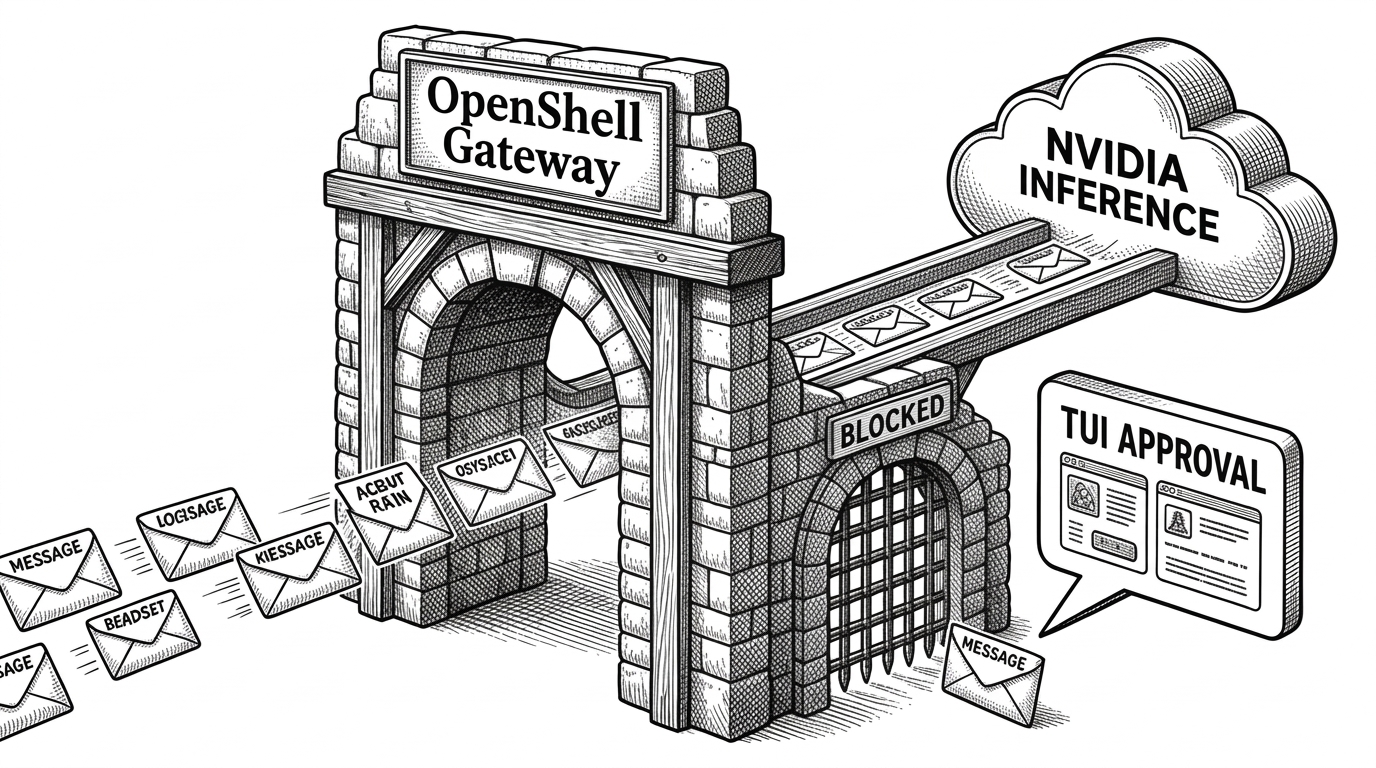
- OpenShell's sandbox using Landlock, seccomp, and network namespaces routes every outbound action through policy checks and human-in-the-loop terminal approvals.
- NVIDIA's reference implementation adds enterprise-grade guardrails to OpenClaw without competing with it, mirroring its earlier PyTorch strategy.
The Security Nightmare Everyone Ignored
OpenClaw exploded to over 320,000 GitHub stars in record time. Jensen Huang called it the operating system for personal AI and said every company now needs an OpenClaw strategy.
The project delivers persistent autonomous agents that code, browse, message, and evolve across sessions. Its viral success proved the hunger for always-on personal AI.
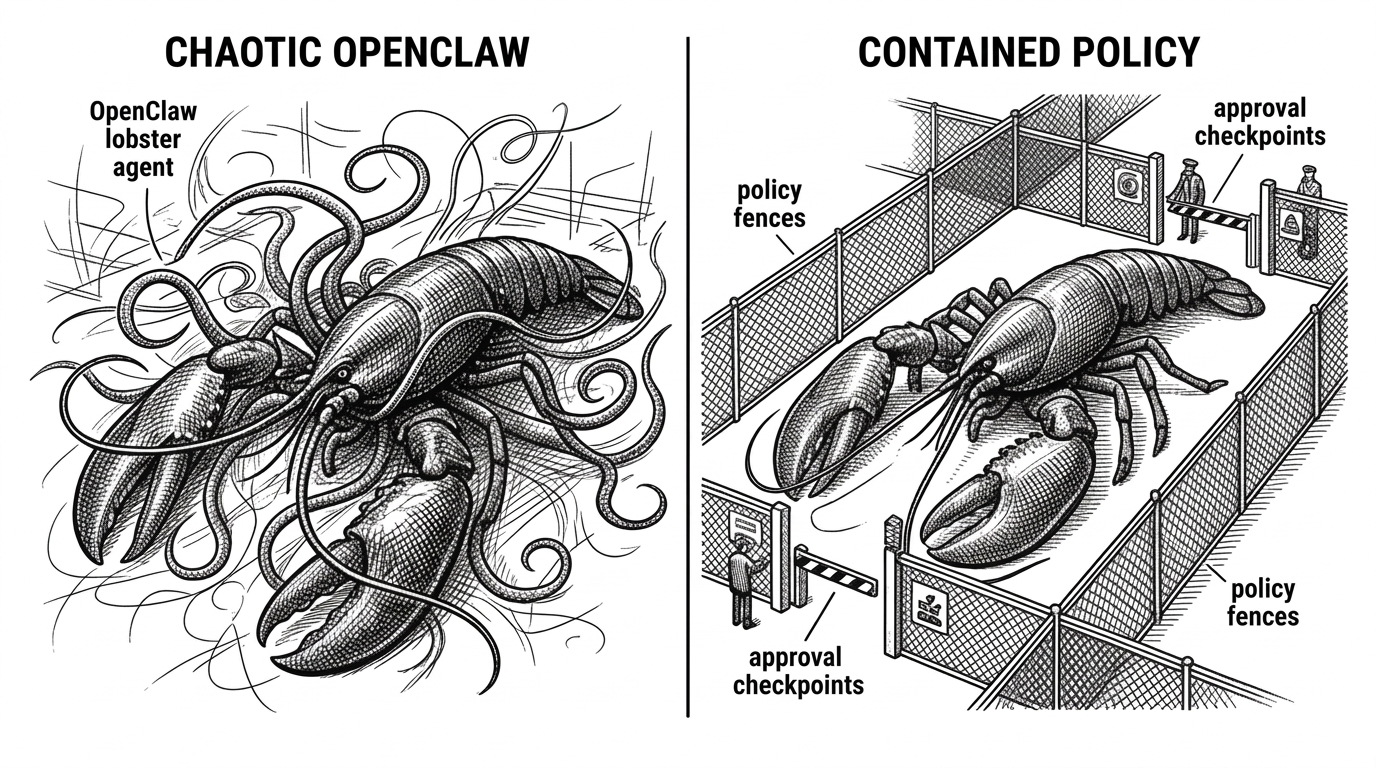
But the same unrestricted power created obvious risks. Agents with broad system access invited prompt injection, data exfiltration, and rogue behavior. Enterprises took one look and said no.
“OpenClaw opened the next frontier of AI to everyone and became the fastest-growing open source project in history. OpenClaw is the operating system for personal AI.”

“With NVIDIA and the broader ecosystem, we’re building the claws and guardrails that let anyone create powerful, secure AI assistants.”
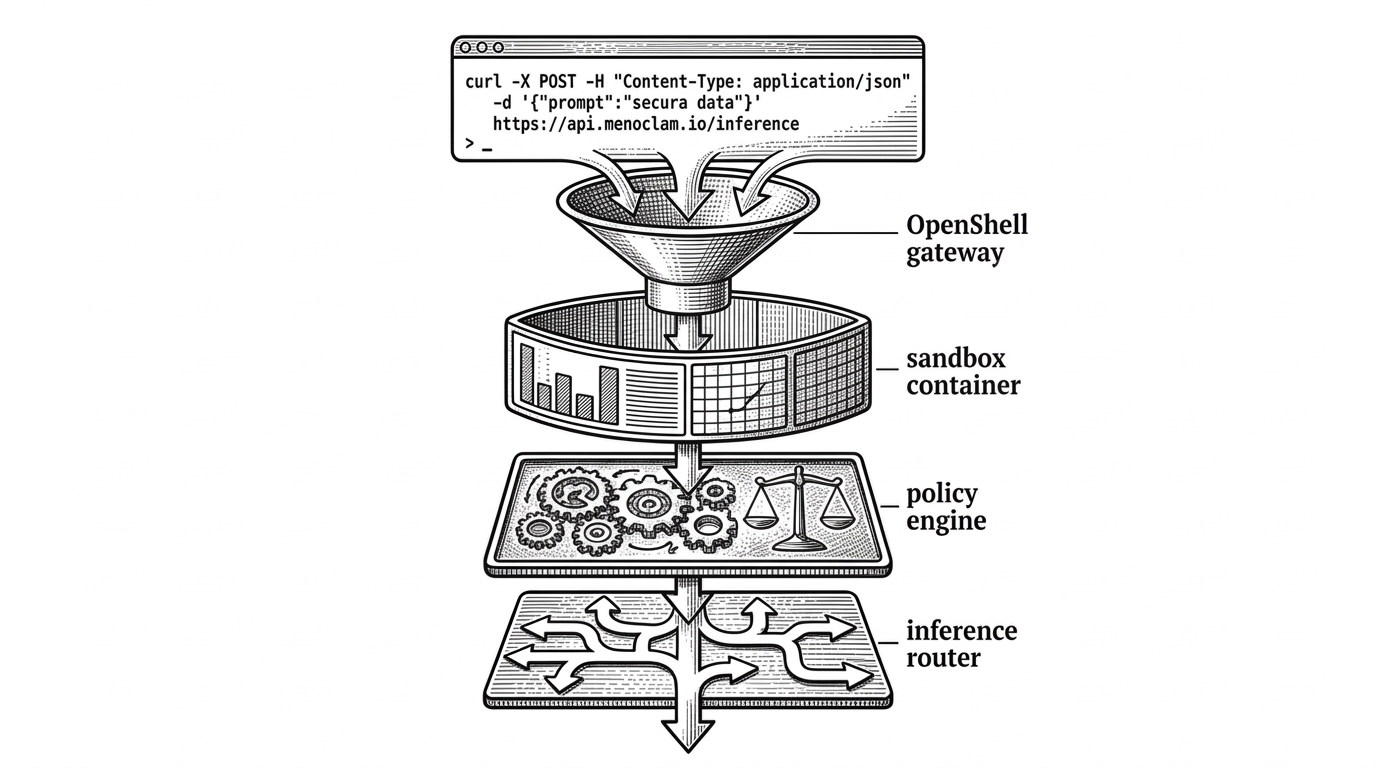
One Curl, Many Layers of Defense
NemoClaw changes the equation with a single command.
curl -fsSL https://nvidia.com/nemoclaw.sh | bashBehind that curl sits a carefully engineered stack. It installs the NVIDIA OpenShell runtime, creates a sandbox using Landlock, seccomp, and network namespaces, and routes inference through controlled channels.
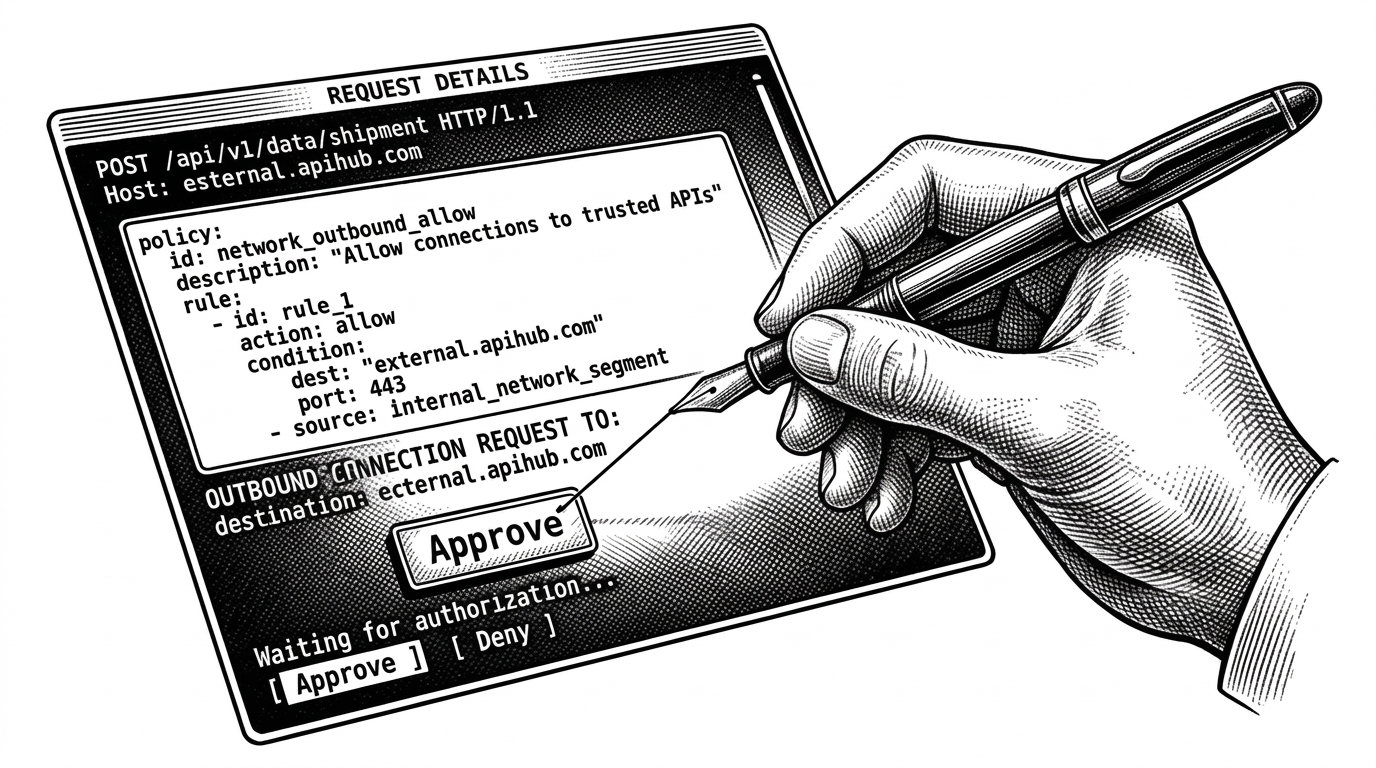
Policy as Code for Agents
The heart of NemoClaw is its declarative YAML policy system. Presets cover common services including PyPI, npm, Slack, Jira, Discord, Telegram, Hugging Face and more.
Network and inference rules are hot-reloadable. Filesystem and process rules remain immutable for stronger guarantees. When an agent attempts an unlisted outbound connection, OpenShell blocks it and surfaces a terminal approval prompt.
The Blueprint Pattern
NemoClaw separates concerns cleverly. A TypeScript CLI provides the user experience while a versioned, signed Python blueprint handles orchestration.
The blueprint follows a strict lifecycle: resolve the artifact, verify its digest, plan required resources, then apply the sandbox through OpenShell. This immutability for core rules combined with hot-reloading for dynamic policies creates a pragmatic balance.
How Different Is It Really?
| Aspect | Raw OpenClaw | NemoClaw | Typical Framework (LangGraph/CrewAI) |
|---|---|---|---|
| Sandboxing | Basic Docker (optional) | Landlock + seccomp + netns via OpenShell | Usually none or minimal |
| Policy Model | None | Declarative YAML with presets | Code-based or absent |
| Installation | Complex setup | Single curl command | pip install + custom config |
| Inference Control | Direct | Routed through gateway with policy | Direct API calls |
| Human Oversight | None | TUI approval for outbound requests | Manual only |
| Target User | Enthusiasts | Production and enterprise | Developers building workflows |
Inside the Sandbox
OpenShell acts as the fortified gateway. Every network request, file operation, process spawn, and inference call passes through policy checks. The TUI makes the approval process feel like a natural extension of the terminal workflow rather than a burdensome security tool.
Extensibility remains intact. The presets handle the common cases while custom policies let operators adapt the system to their environment.
NVIDIA's Bigger Bet
NemoClaw is not a competitor to OpenClaw. It is NVIDIA's reference implementation for making the phenomenon safe enough for real use. The collaboration with Peter Steinberger shows the project's community-first approach.
This mirrors NVIDIA's earlier playbook with PyTorch: contribute critical infrastructure to an open movement while advancing its own hardware and cloud offerings. Jensen Huang's enthusiastic framing at GTC positions claws as the next major computing platform.
“OpenClaw brings people closer to AI and helps create a world where everyone has their own agents. With NVIDIA and the broader ecosystem, we’re building the claws and guardrails that let anyone create powerful, secure AI assistants.”